Syslog Server – a time saving tool
Today I’m writing about a use case, which is not very popular amongst IT professionals. Troubleshooting by parsing system logs. Sounds attractive as a dental surgery.
Almost any system and any component logs events, warnings and errors into some kind of internal log. Emphasis is on any and internal, because that’s part of the problem. Log information isn’t usually easy accessible. And once you’ve copied all logs to a common location, you need to scroll through it by a text editor. This is cumbersome and tricky. If you – for example – have to align events from a server with events from a switch, you’ll need multiple steps to achieve it. A very time-consuming procedure. If you have bad luck (Murphy says, you will..), one of the components is unavailable, because an error occurred. No log – no analysis.
What’s the benefit of a syslog tool?
To avoid situations like the one outlined above, there are syslog servers such as Graylog, Kiwi, Splunk or PRTG, which can aggregate information from different sources. But just by installing a syslog server the job is not yet done. You need to filter relevant information from the flood of data. One of the main reasons why so many syslog rollout projects fail. They will be bought, installed and forgotten.
Single pane of glass
One of the most important features of a syslog server is the ability to collect all information from different sources an display them on a single pane of glass.
Data Processing
A second important feature of a good syslog system is intelligent processing and visualization of the data. I do expect that the software filters all the junk and keeps me focused on important information.
Retention time
Syslog systems usually have longer event retention times than the source systems. Many servers, appliances and hardware components use logrotation to save local storage capacity. After a certain time or a defined size of the logfile it will be compressed and archived. The number of archives is fixed and once a new one is added, an old one will be deleted. This way sometimes valuable information get lost. How often in the past did a certain message occur and when was it’s first appearance?
Permanent storage
Besides retention time, permanent storage is an important feature. Some hardware appliances keep their logs in non-persistent storage. After a reboot they’re gone. By exporting these messages to a syslog server you can save them on permanent storage.
VMware vRealize Log Insight
While searching for a syslog solution one might not see the obvious. VMware offers Log Insight as part of its vRealize suite. It unites all the requirements I’ve outlined above. It collects data from the VMware ecosystem, but also from third party software, servers, switches etc. Data gets processed, grouped and visualized by an intelligent architecture. That enables fast and efficient troubleshooting. Events from the virtual infrastructure can be easily correlated to events from physical hardware. By defining custom filters, every user can build his own dashboard to have all relevant data on a single page.
Log Insight is a very versatile yet often underestimated tool for troubleshooting.
Licensing
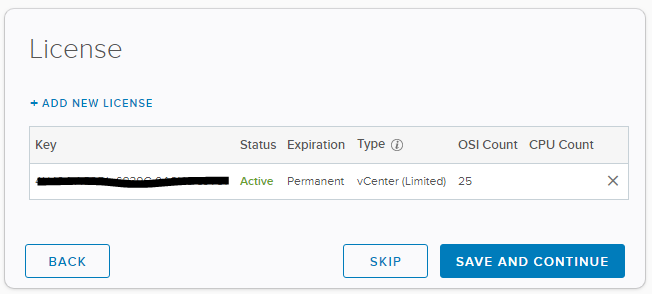
Syslog tools usually impose considerable cost. Isn’t it pleasant to hear, that the standard license for Log Insight is already included in a vCenter license? If you own a valid vCenter license, you’re entitled to a free 25 OSI (operation system instances) license of Log Insight. Use your vCenter license to activate the product. It even works with an Essential-Plus package.
Editions
With a vCenter license you get a free log Insight license. Content packs for all kinds of VMware products are included. If you want to install 3rd party content packs from the internal marketplace, you’ll need the Enterprise edition.
Setup
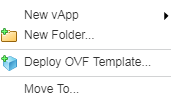
Installation of vRealize Log Insight is simple. You can download the appliance from VMware’s download site and deploy it with the vSphere-Client or the Web-Client. Select “Deploy OVF Template”
Point to a local source and select the OVA file you’ve downloaded before.
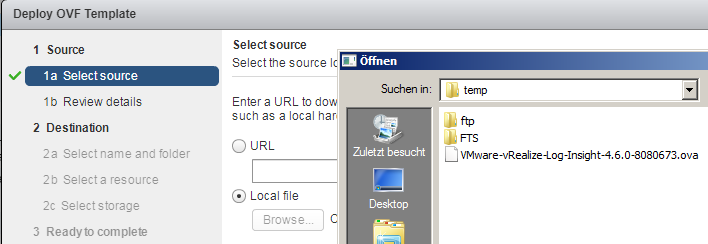
All necessary configuration parameters can be entered within the deployment wizard.
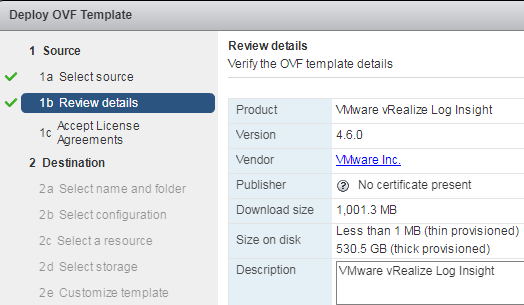
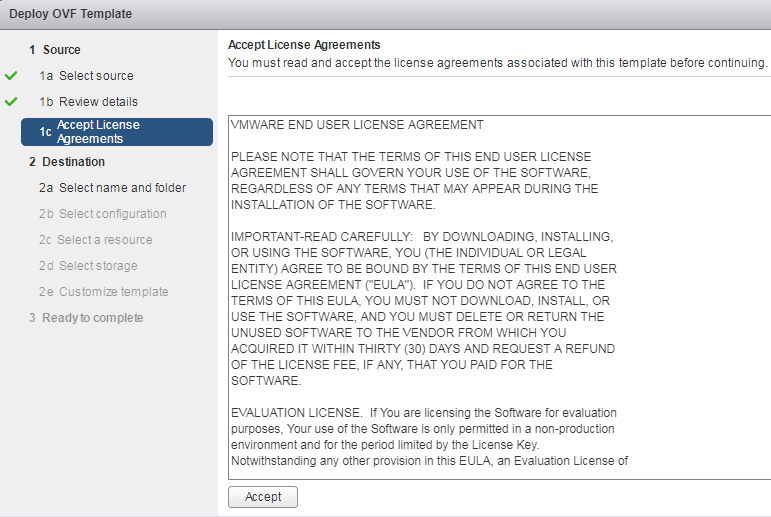
First accept the EULA.
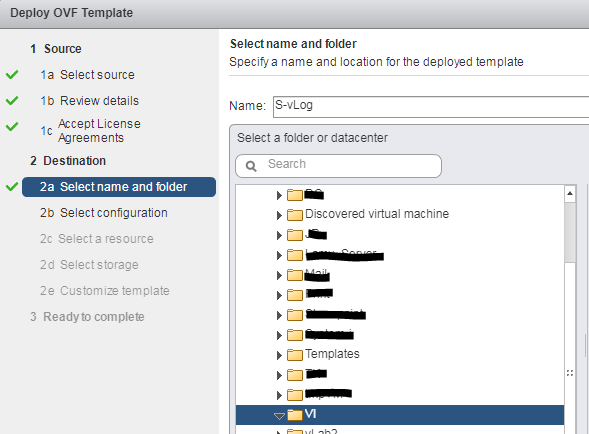
Define a VM-name and select a destination folder.
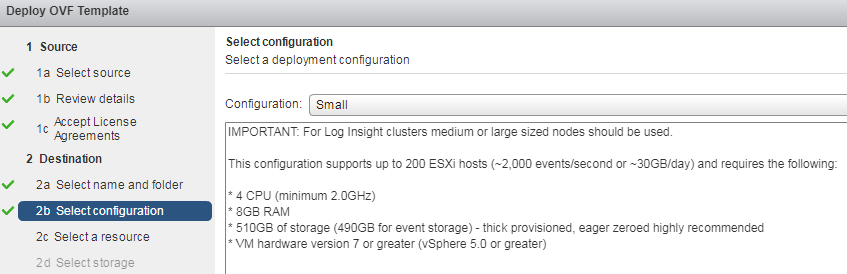
Depending on the size of the environment you’re going to monitor, you can choose between different configurations. For an appliance with up to 25 agents you should be fine with “Small”. There’s more information in the wizards help text.
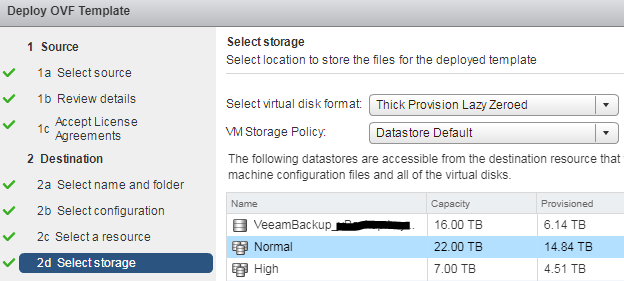
Next step is to select a datastore and a disk format for the appliance.
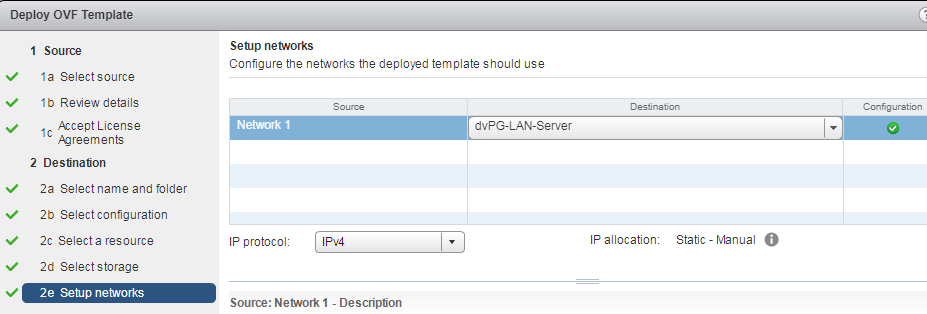
Map the appliance’s native portgroup “Network 1” to your destination portgroup. In my example it is a distributed portgroup on a dvSwitch.
Finally the appliance will be deployed to the cluster and configured with your settings.
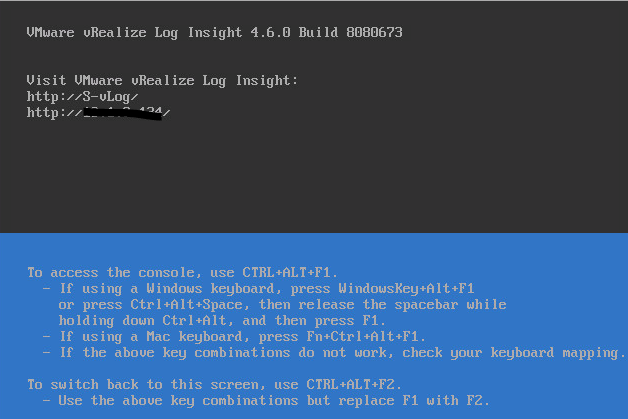
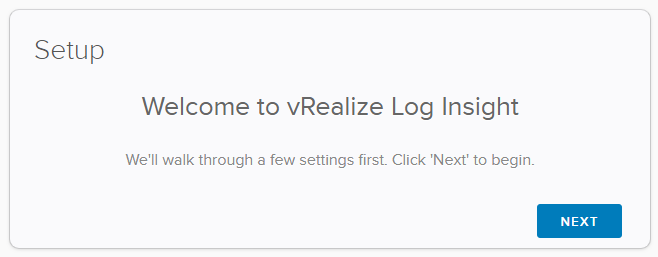
As soon as the black and blue screen appears you can log in with a browser and finalize the setup.
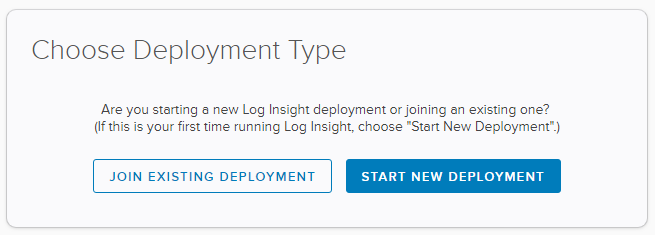
If it is a new deployment, select “Start new deployment”.
Another wizard will ask some more questions about the environment.
You can enter your existing vCenter license. There’s no need for a special license unless you plan to use enterprise features.
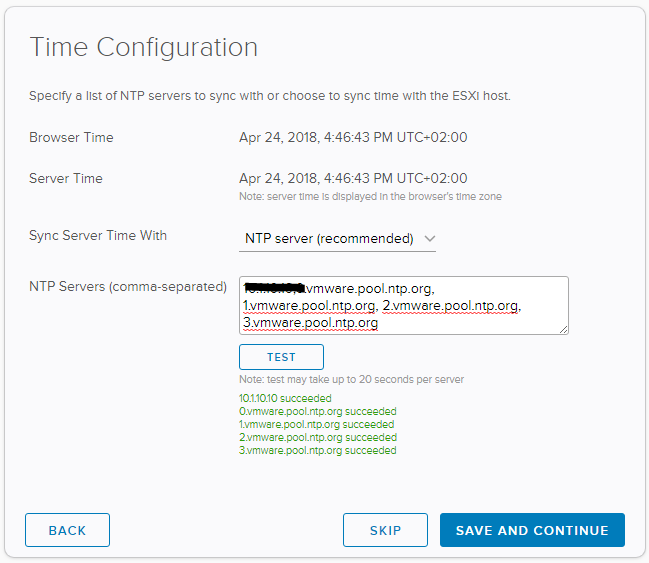
Having a time source is important to correlate events. The wizard proposes some public NTP servers, but you can add timeservers of the intranet too. Enter either FQDN or IP address.
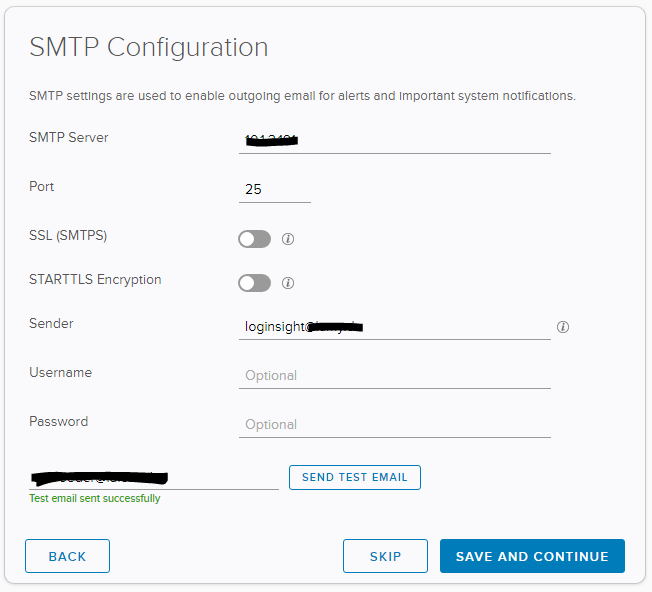
To send email notifications you need to enter your SMTP server.
Almost done…
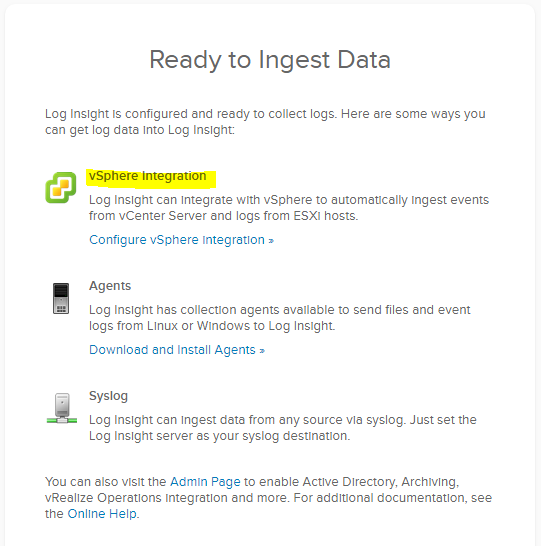
Now we need to integrate vCenter and the ESXi hosts (vSphere Integration). Linux and Windows hosts can be integrated by agents. Syslog receives messages over syslog protocol.
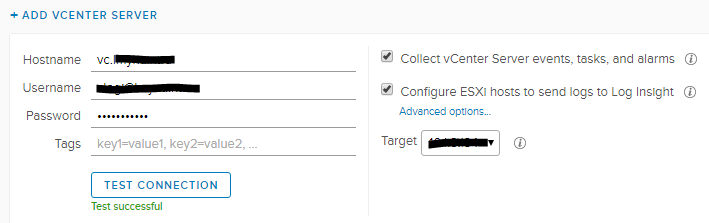
First let’s configure vCenter integration. It’s also a good idea to check the option “Collect ESXi hosts to send logs to Log Insight”. ESXi host will then be configured to send their logs directly to the Log Insight appliance.
Content Packs
There are a couple of addons for Log Insight, called Content Packs. A selection of third party packs is available from internal marketplace (Enterprise feature) or from the marketplace website. You can also define and load own packs (Enterprise feature). For example there’s a Veeam Content Pack to monitor backup jobs and results within Log Insight.
Links
- VMware vRealize Log Insight Datenblatt
- VMware Log Insight Produktübsersicht
- VMware KB 2144909 – FAQ: Log Insight for vCenter Server
- VMware Marketplace – vRealize Log Insight Content Pack

